
Happy National OSINT Day! To celebrate, my article for you all today is a career map. One of the best things about OSINT is how many different directions you can take it, and one of the most common questions from people interested in the field is “where do I actually start?” This is designed to help you answer that.
Most of us working in Open-Source Intelligence (OSINT) didn’t start there. We come from all over (diverse backgrounds, work histories, and industries). I started out as a HUMINT collector in the Army. (And if you’d told me then that I would be in OSINT now, doing technical and computer-based things, I wouldn’t have believed you.) Some of the top OSINT practitioners started in journalism, accounting, IT, law enforcement, military service, and academic research. They discovered that the skills they’d already built were exactly what OSINT work required. There’s no single entry point or standard career ladder, which means whatever you’re already good at connects to a role you haven’t considered yet.
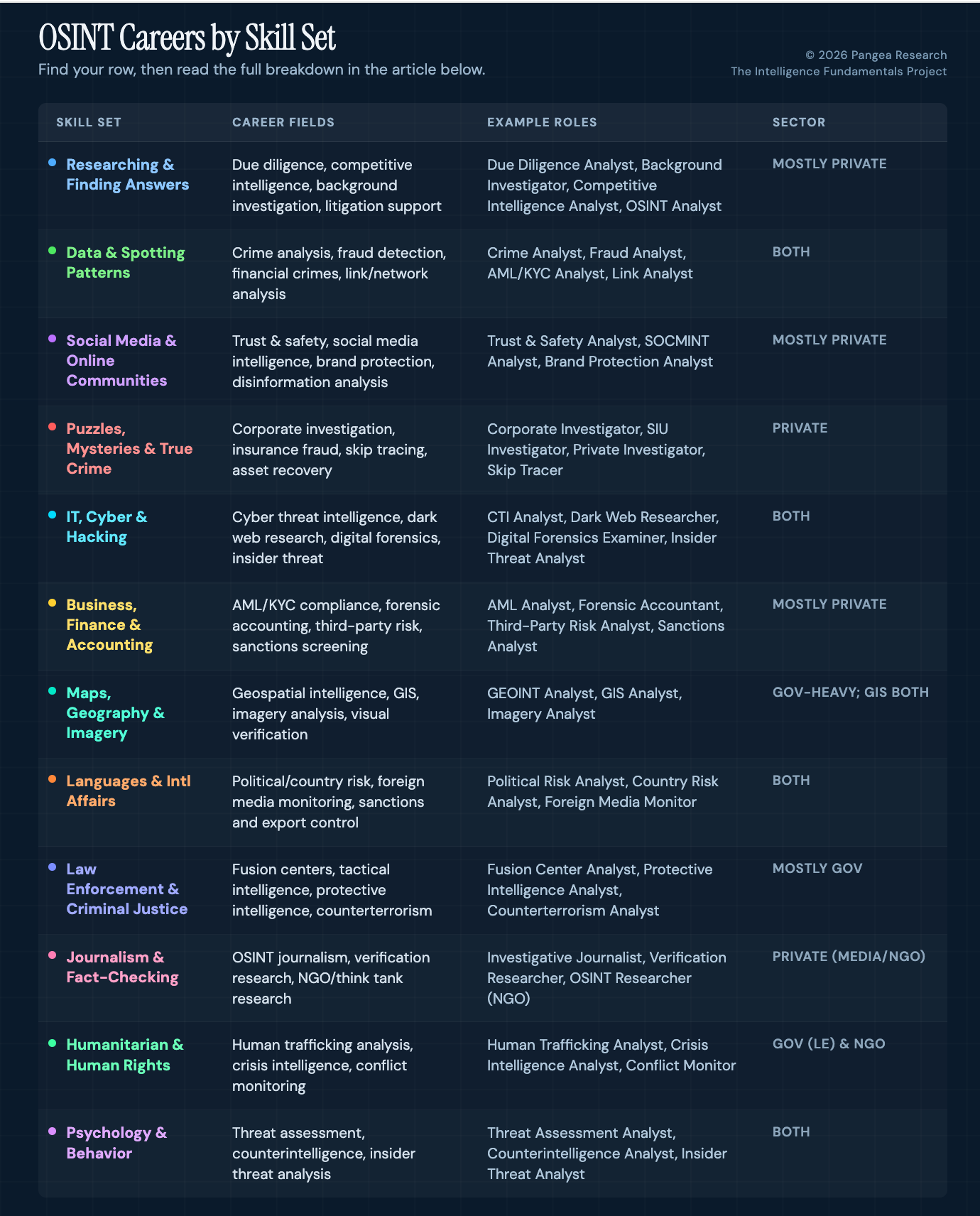
This article walks through twelve categories of skills and interests that translate directly into OSINT and OSINT-adjacent career fields. Some require security clearances and sit inside government agencies; others are private sector and open to anyone with the right skills; some exist in both. Each section describes what the work involves day-to-day, who hires for it, and what kind of background translates well. If you’ve been wondering how your experience connects to this world, one of these sections probably covers it.
Find your row in the table below, then jump to that section for the full breakdown of what the work looks like and how people get into it.
A note on job titles: they aren’t standardized in this field. The same work might be called “OSINT Analyst” at one company, “Research Analyst” at another, and “Intelligence Specialist” at a third. Some roles appear in more than one category because they draw on multiple skill sets; a Financial Crimes Analyst shows up under both “data and patterns” and “business and finance” because the job requires both. Each section below focuses on what the work involves regardless of what it’s titled.
If You Liked Researching and Finding Answers
If you were the person in college staying up until 2 a.m. because you hadn’t finished chasing a question through the library database, you’ll find OSINT work satisfying for the same reasons. Someone needs to know something, and your job is to find it, verify it, and deliver it in a form they can act on. The questions are harder, the stakes are higher, and the sources are messier than anything you encountered in school.
Due diligence is one of the largest and most accessible entry points into OSINT-adjacent work. Due diligence analysts at corporate intelligence firms spend their days investigating companies, individuals, and transactions on behalf of clients considering investments, partnerships, or acquisitions. A typical assignment might involve tracing a company’s ownership through multiple jurisdictions, identifying undisclosed litigation, or flagging connections between a prospective business partner and sanctioned entities. The work is methodical: you’re pulling corporate registrations, court records, regulatory filings, property records, and media coverage, then synthesizing all of it into a report that helps someone decide whether to put money on the table. Firms like Kroll, Control Risks, Nardello & Co., and dozens of smaller consultancies hire for these roles, and they value research skills over clearances or prior government experience.
Background investigation is closely related but focused on individuals rather than corporate entities. Government background investigators (working for agencies like DCSA, formerly NBIB) conduct the investigations that determine whether someone gets a security clearance. Private-sector background investigators work for law firms, corporate security departments, and investigation agencies. In both cases, the work is record-intensive: you’re verifying employment history, checking criminal and civil court records, running financial checks, and interviewing references.
Competitive intelligence sits inside corporations rather than consulting firms. Competitive intelligence analysts track competitors’ moves through public filings, patent applications, job postings, trade publications, and industry conferences. If a competitor files a patent for a new manufacturing process, hires three engineers from a specific subfield, and opens a new facility in a particular region, a competitive intelligence analyst connects those dots and tells leadership what it means for their strategy. The same analytical process applies to litigation support and eDiscovery, where analysts piece together the facts of legal disputes using court filings, public records, and open-source investigation.
These research-heavy fields are predominantly private sector, and most don’t require clearances. Due diligence and competitive intelligence in particular hire people from a wide range of academic backgrounds; they’re looking for someone who can chase a question to its answer and communicate what they found clearly.
If You Liked Working with Data and Spotting Patterns
Some people are drawn to OSINT because they like finding information, and others because they like what happens after: organizing it, mapping connections, and identifying patterns that aren’t visible in any single source. If you were the person in your previous job who built the spreadsheet that revealed the trend no one else noticed, this is where your skills connect.
Crime analysis is the law enforcement application of this skill set. Crime analysts work in police departments, sheriff’s offices, and fusion centers (multi-agency intelligence centers that share information across jurisdictions). Their work involves collecting data on criminal incidents, mapping patterns geographically and temporally, identifying suspect networks, and producing intelligence products that help patrol officers and detectives allocate their time. If burglaries in a district cluster around specific hours, locations, and methods, the crime analyst identifies that pattern and translates it into actionable guidance for the officers working those areas. These positions exist at city, county, state, and federal levels, and many are accessible without prior law enforcement experience, particularly at the local level. The International Association of Crime Analysts (IACA) maintains job boards and certification programs that are a recognized entry pathway.
Fraud analysis and financial crimes investigation are the private sector equivalents, concentrated in banking, insurance, and financial services. Fraud analysts review transactions and account activity to detect patterns that indicate fraud, money laundering, or sanctions evasion. Anti-money laundering (AML) and know-your-customer (KYC) analysts are specific variations of this work, focused on regulatory compliance in financial institutions. The day-to-day involves reviewing alerts generated by automated monitoring systems, investigating flagged transactions, documenting findings, and filing Suspicious Activity Reports (SARs) when the evidence warrants it. These roles are plentiful because every major bank and financial institution is required by law to maintain compliance programs, and those programs need analysts. For someone coming from a data or accounting background, AML/KYC analysis is one of the highest-volume entry points in the entire OSINT-adjacent job market.
Link and network analysis sits at the more specialized end of this category. Link analysts build visual maps of relationships between people, organizations, phone numbers, financial accounts, addresses, and other data points. A law enforcement link analyst might map a drug trafficking network by connecting phone records, financial transfers, surveillance data, and arrest records. A corporate link analyst might map a company’s ownership structure across multiple jurisdictions to determine who ultimately controls it. The tools vary (Analyst’s Notebook, Maltego, Palantir, or even manual charting), but the skill is the same: looking at a pile of data points that individually mean little and identifying the structure that connects them.
If You Liked Social Media and Online Communities
Understanding how people behave online, how information spreads, how communities form and fracture, and how platforms work at a technical level is a skill set that maps to a growing number of OSINT-adjacent careers. If you spent years moderating forums, building online communities, studying platform dynamics, or just paying close attention to how content moves through networks, those skills have professional applications.
Trust and safety is one of the fastest-growing fields in this category. Trust and safety analysts work at technology companies (Google, Meta, TikTok, Discord, OpenAI, Reddit, and others) where they investigate platform abuse, enforce content policies, detect fraud, and identify emerging patterns of harmful behavior. The work involves reviewing flagged content and accounts, investigating coordinated manipulation campaigns, analyzing data to identify abuse trends, and recommending policy or product changes based on what they find. Compensation is strong (median total compensation around $108,000 according to Glassdoor data from 2025), and the field is expanding because every platform that hosts user-generated content needs people who understand how abuse works at scale. Trust and safety roles are entirely private sector and don’t require clearances; they value platform literacy, analytical skills, and the ability to make judgment calls under ambiguity.
Some organizations label social media research as "SOCMINT" (social media intelligence), and you'll see the term in job postings, organizational charts, and conference agendas. Analysts in these positions monitor online activity for threats against executives or facilities, track brand risks, or collect intelligence relevant to their organization’s mission. A corporate security department might hire someone with “SOCMINT” in the title to monitor social media for threats against company leadership, while a government agency might use the same label for analysts tracking extremist groups’ online recruitment activity.
Note: SOCMINT is not a separate intelligence subdiscipline in the United States; it's a research category within OSINT that some practitioners and organizations have adopted as its own label. It IS a discipline in some other countries, so knowing it helps when you're searching for roles because employers do use it.
Brand protection analysts do related work focused on intellectual property: identifying counterfeit products being sold online, tracking unauthorized use of trademarks, and documenting evidence for enforcement actions. Brand protection is a growing field because the scale of online counterfeiting has exploded with the proliferation of e-commerce platforms, and companies need people who understand how counterfeiters operate across different platforms and jurisdictions.
If You Liked Solving Puzzles, Mysteries, or True Crime
If you’re the person who reads case files for fun, reconstructs timelines from scattered evidence, or finds satisfaction in locating someone or something that’s been deliberately hidden, investigation roles are a natural fit. These positions reward persistence, lateral thinking, and knowing where to look when the obvious sources come up empty.
Corporate investigation covers a wide range of work performed for companies, law firms, and investigation agencies. Cases range from internal fraud to intellectual property theft to pre-litigation research. A corporate investigator might spend a week tracing assets that a defendant has moved through shell companies to avoid a judgment, or documenting that a former employee took proprietary files when they left. Private investigators do similar work, often for individuals, attorneys, or insurance companies.
Insurance fraud investigation (often performed by Special Investigations Unit or SIU investigators) is a large and stable subfield. SIU investigators work for insurance carriers, investigating claims that appear fraudulent. If someone files a disability claim but their social media shows them running a marathon, the SIU investigator finds and documents that evidence. The work requires attention to evidentiary standards because the documentation has to hold up if the case goes to court. Insurance carriers hire SIU investigators in volume, and the work translates well to other investigative roles because it teaches you to build a case methodically using open sources.
Skip tracing and asset recovery are specialized investigative fields that rely heavily on OSINT. Skip tracers locate people who don’t want to be found, typically for debt collection, legal service of process, or bail enforcement. Asset recovery specialists track and recover assets that have been hidden, moved, or fraudulently transferred. Both roles depend on public records research, database searches, and creative problem-solving that comes from understanding how people try to disappear and where those efforts leave traces. Missing persons investigators work in both law enforcement and the private sector, and their work ranges from locating runaway teenagers to finding adults who have intentionally cut contact with family members.
Many investigative roles require or benefit from a private investigator license, which varies by state but generally involves a combination of experience, examination, and background check. The investigative pathway is overwhelmingly private sector, and entry often comes through investigation firms, insurance companies, or law firms that need research support.
If You Liked IT, Cybersecurity, or Hacking
Cyber threat intelligence (CTI) is where OSINT and cybersecurity overlap most directly. If you liked building networks, breaking into systems (legally), analyzing malware, or understanding how attackers operate, there’s a well-established set of career fields that combine those technical skills with intelligence analysis methods.
CTI analysts collect, analyze, and report on threats to their organization’s digital infrastructure. The work involves monitoring threat actor groups, analyzing malware samples, tracking indicators of compromise (IP addresses, domain names, file hashes, and other technical fingerprints that indicate a specific threat), and producing intelligence reports that help security teams prioritize their defenses. A CTI analyst might identify that a ransomware group has shifted its targeting from healthcare to manufacturing, analyze the group’s tools and techniques, and brief the security operations team on what to watch for. These roles exist at companies of every size that take cybersecurity seriously, as well as at dedicated threat intelligence firms like Recorded Future, Mandiant, CrowdStrike, and Flashpoint.
Dark web research is a specialization within CTI focused on monitoring forums, marketplaces, and communication channels on the dark web for threats relevant to the organization or its clients. This might involve tracking the sale of stolen credentials, monitoring for leaked proprietary data, or identifying threat actors discussing targeting specific industries or companies. The work requires familiarity with dark web infrastructure, cryptocurrency tracing, and operational security.
Digital forensics is the investigative side of this field: recovering and analyzing data from computers, phones, and other digital devices in support of investigations. Digital forensics examiners work in law enforcement, consulting firms, and corporate security departments, supporting cases that range from employee misconduct to criminal prosecution to civil litigation.
Insider threat analysis sits at the intersection of cybersecurity and behavioral analysis. Insider threat analysts detect and investigate threats that originate inside an organization, combining technical monitoring (who accessed what data, when, and from where) with behavioral analysis (is this person under financial stress, expressing grievances, or behaving in ways that correlate with data exfiltration). The work requires both technical literacy and an understanding of human motivation, which is why insider threat programs often hire people from diverse backgrounds and cross-train them.
CTI, dark web research, digital forensics, and insider threat analysis all exist in both government and private sector, with private sector roles generally more accessible. The cybersecurity talent shortage means these fields hire actively, and many employers will train candidates who bring strong analytical skills from adjacent fields.
If You Liked Business, Finance, or Accounting
Financial investigation is one of the largest and most accessible areas of OSINT-adjacent work because every bank, investment firm, and financial institution is legally required to maintain programs that detect money laundering, fraud, and sanctions violations. Those programs need people, and the skills involved (following money through records, understanding corporate structures, identifying discrepancies in financial data) map directly to accounting, auditing, and business analysis backgrounds.
AML and KYC compliance is where most of the volume sits. When a bank onboards a new corporate client, a KYC analyst researches the company’s ownership structure, identifies the ultimate beneficial owners, checks those individuals against sanctions lists and adverse media, and documents the findings. When the monitoring system flags a series of wire transfers that follow a pattern associated with money laundering, an AML analyst reviews the transactions, investigates the parties involved, and determines whether a Suspicious Activity Report needs to be filed with the Financial Crimes Enforcement Network (FinCEN). These roles are available in large numbers at every major financial institution, and many employers will train new hires on the regulatory framework if they bring strong research and analytical skills. For someone trying to break into OSINT-adjacent work without a clearance or prior intelligence experience, AML/KYC analyst roles at a bank are one of the most practical starting points.
Due diligence (also covered in the research section) is particularly relevant for business and finance backgrounds because the work often involves reading and interpreting financial statements, understanding corporate structures across jurisdictions, and evaluating risk in terms that business decision-makers understand. Third-party risk analysis is a related field that evaluates the risk a company’s vendors, suppliers, and business partners pose to the organization, using a combination of financial analysis, regulatory research, and open-source investigation.
Forensic accounting combines accounting expertise with investigative skills to trace funds, detect financial fraud, and support litigation. Forensic accountants work at consulting firms, law enforcement agencies (the FBI, IRS Criminal Investigation, and SEC all employ them), and corporate internal audit departments. The work involves mapping the flow of capital across international borders, analyzing shell company structures, and identifying discrepancies that suggest embezzlement, tax evasion, or bribery. Forensic accounting requires accounting credentials, but for someone who already has them, it’s one of the more direct paths into investigative work.
If You Liked Maps, Geography, or Satellite Imagery
Geospatial intelligence (GEOINT) has expanded well beyond its military origins. Commercial satellite imagery is now available at resolutions that were classified a generation ago, and the tools for analyzing it are accessible to anyone willing to learn them. If you studied geography, GIS, remote sensing, or environmental science, or if you’re just the person who zooms into satellite imagery to understand how a place is laid out, there’s a professional path here.
Government GEOINT work involves analyzing satellite imagery, aerial photography, and other geospatial data to answer intelligence questions: what’s being built at this facility, how has this military installation changed over the past six months, where are displaced populations moving. The National Geospatial-Intelligence Agency (NGA) and military intelligence units are the primary employers, and these roles require clearances and are harder to access without prior government experience or military service.
GIS analysis is the more broadly accessible version of this skill set. GIS analysts work across government and private sector organizations, managing geographic data, building maps and spatial databases, and conducting spatial analysis. The title “GIS Analyst” appears in law enforcement (mapping crime patterns), urban planning, environmental consulting, logistics, insurance, and dozens of other industries, making it one of the more versatile entry points for people with geospatial skills. A GIS background combined with OSINT research methods gives you a skill combination that’s directly applicable to fields ranging from corporate security to humanitarian response.
Imagery analysis and visual verification have gained visibility through the work of organizations like Bellingcat, which pioneered techniques for verifying the location and date of photos and videos using satellite imagery, street-level photography, shadow angles, and architectural features. These geolocation and chronolocation techniques are now standard practice in journalism, human rights documentation, legal proceedings, and corporate investigations. In a government context, an imagery analyst might study satellite photos of a foreign military base. In a civilian context, the same skills apply to verifying user-generated content from a conflict zone, analyzing drone footage for an insurance claim, or examining surveillance video for a corporate investigation.
If You Liked Foreign Languages and International Affairs
Language skills and regional expertise create OSINT career paths that monolingual analysts can’t access. If you studied a foreign language seriously, lived abroad, or focused on international relations, area studies, or comparative politics, you bring something that tools and technology can’t replicate: the ability to read, interpret, and contextualize information in its original language and cultural setting. Machine translation has improved dramatically, but it still misses cultural nuance, localized slang, historical context, and the implicit biases embedded in foreign-language media. Analysts who can work directly in the source language catch things that automated tools miss.
Political and country risk analysis is the primary private sector field for this skill set. Political risk analysts at consulting firms monitor developments in countries where clients have operations, tracking legislative changes, political instability, labor unrest, and security threats that could affect the client’s business. Country risk analysts at banks and financial institutions assess whether regulatory, political, or economic conditions in a given country create risks for the institution’s transactions and counterparties. Both fields value language skills and regional knowledge over clearances, and the hiring is concentrated at consulting firms, financial institutions, and corporations with international exposure.
Foreign media monitoring is a field with deep roots in the intelligence community. The CIA’s Open Source Enterprise (formerly the Foreign Broadcast Information Service) spent decades translating foreign media for the intelligence community, and that function now extends to private sector firms that monitor global media for corporate clients. Analysts in these roles read, translate, and summarize news and commentary from foreign-language sources, providing their organizations with a window into how events are being reported and interpreted in other countries.
Sanctions and export control analysis is a compliance-oriented field where language skills provide a concrete operational advantage. Sanctions analysts evaluate whether transactions, individuals, or entities are subject to sanctions programs administered by the U.S. Treasury’s Office of Foreign Assets Control (OFAC) or similar bodies in other countries. The subjects of investigation often operate through entities with names in languages other than English, and understanding the original-language records can reveal transliteration discrepancies, localized naming conventions, and obfuscated ownership structures that English-centric screening algorithms miss entirely.
If You Liked Law Enforcement or Criminal Justice
People with law enforcement or criminal justice backgrounds (or academic interest in those fields) find that many of the concepts they’ve studied map directly to intelligence analysis roles, particularly at the state and local level where fusion centers and crime analysis units are the primary intelligence infrastructure.
Fusion centers are one of the most accessible entry points into government intelligence work. There are roughly 80 state and regional fusion centers across the United States, and they are multi-agency intelligence operations that share information across law enforcement, public safety, and homeland security agencies. Because fusion centers hire at the state and local level, they don’t always require federal clearances, which removes one of the biggest barriers to government intelligence careers. The work involves collecting and analyzing information from law enforcement databases, public records, and open sources to produce intelligence products that support investigations, threat assessments, and situational awareness for partner agencies.
Tactical intelligence analysis and crime analysis (covered in the data section above) sit within law enforcement agencies, directly supporting operations. Protective intelligence is a specialized field focused on identifying and assessing threats against individuals or facilities. Protective intelligence analysts work in government (the Secret Service, Capitol Police, and similar agencies) and in private sector corporate executive protection programs, where they monitor for threats against company leadership and facilities. The field draws on OSINT, behavioral analysis, and threat assessment methods, and it’s one of the areas where law enforcement and private sector security overlap most directly.
Counterterrorism analysis exists at federal, state, and local levels. Counterterrorism analysts monitor and analyze information related to terrorist threats and produce assessments that inform prevention and response efforts. At the federal level, these roles require clearances and prior intelligence experience. At the state and local level, particularly within fusion centers, counterterrorism analysis roles are more accessible, though they still require a solid understanding of threat assessment methods and the ability to work with information from multiple intelligence disciplines.
If You Liked Journalism or Fact-Checking
Journalists and fact-checkers already do a version of OSINT work: they find sources, verify information, assess credibility, and present findings to audiences who need to make informed decisions. The crossover is direct, and several organizations now explicitly hire for OSINT skills in newsrooms and research teams.
OSINT-focused investigative journalism uses the same techniques as intelligence analysis (public records research, geolocation, social media investigation, corporate structure tracing, satellite imagery analysis) and applies them to accountability reporting. Bellingcat, the Global Investigative Journalism Network, and the Organized Crime and Corruption Reporting Project (OCCRP) are among the organizations that have built investigative capacity around these methods. The advantage of OSINT-based journalism is that it doesn’t depend on authorized inside sources or official access; investigations can be built entirely on public procurement databases, flight tracking data, maritime transponder records, corporate filings, and satellite imagery.
Verification research and fact-checking is a related field focused on determining whether user-generated content (photos, videos, social media posts) is authentic and accurately described. During breaking events (natural disasters, conflicts, mass casualty incidents), verification specialists determine which images and reports circulating on social media are genuine and which are recycled, manipulated, or fabricated. This work requires fluency with reverse image searching, metadata extraction, geolocation techniques, and an understanding of how misinformation spreads across platforms.
OSINT researchers at non-governmental organizations and think tanks apply similar skills to human rights documentation, conflict monitoring, environmental monitoring, and accountability work. Organizations like Amnesty International, Human Rights Watch, the Atlantic Council’s Digital Forensic Research Lab, and the Centre for Information Resilience hire researchers who combine OSINT skills with subject-matter expertise. These roles often pay less than corporate or government positions, but the published output (investigations, reports, datasets) builds a public portfolio that other employers in the field recognize, and many practitioners use NGO and journalism experience as a springboard into government or corporate intelligence roles.
The hiring pipeline for journalism and NGO OSINT roles differs from other fields on this map. Portfolio work, published investigations, and demonstrated OSINT skills matter more than degrees or certifications. Contributing to open-source investigations, publishing findings on personal blogs or collaborative platforms, and participating in crowd-sourced verification projects are all recognized ways to build credibility with these organizations.
If You Liked Helping People or Humanitarian Work
OSINT skills apply directly to humanitarian and human rights work, and several organizations have built dedicated analytical capabilities around open-source methods. If you studied international development, public health, humanitarian aid, or human rights and you want analytical work in service of those missions, the roles below sit at that intersection.
Human trafficking analysis is one of the most direct applications. Human trafficking analysts work in both law enforcement (the FBI, DHS, and state and local task forces) and non-governmental organizations, using open-source research to identify trafficking networks, locate victims, and support prosecutions. The work involves monitoring online advertisements, tracing phone numbers and email addresses, analyzing financial transactions, and mapping networks that span multiple jurisdictions. Child exploitation investigation (performed through Internet Crimes Against Children task forces, the National Center for Missing & Exploited Children, and law enforcement agencies) uses similar techniques to identify offenders and victims in online child exploitation cases. Both fields are emotionally demanding and require institutional support for the people doing the work; organizations vary significantly in how well they provide that support, and it’s worth asking about before accepting a position.
Humanitarian and crisis intelligence analysis serves international organizations (the United Nations Office for the Coordination of Humanitarian Affairs, the International Committee of the Red Cross, Médecins Sans Frontières) and NGOs. During a natural disaster or armed conflict, these analysts monitor open sources (social media, news reports, satellite imagery, government statements) to track the evolving situation and help their organizations allocate resources and make operational decisions. Conflict monitors at organizations like the Sudan Human Rights Hub or the Centre for Information Resilience use geolocation, chronolocation, and metadata analysis to document events for accountability purposes, producing evidence that can be used in legal proceedings or international investigations.
The hiring pipeline for humanitarian OSINT roles is distinct from corporate or government intelligence. Relevant academic background (international humanitarian law, human rights, conflict studies), language skills, field experience, and familiarity with humanitarian coordination frameworks carry more weight than clearances or technical certifications. Many people enter this field through volunteer analytical work with organizations like Bellingcat, Trace Labs (which runs missing persons CTF events), or humanitarian OSINT teams that mobilize during crises.
If You Liked Psychology or Understanding Why People Do What They Do
Threat assessment analysts evaluate whether individuals who have made threats or displayed concerning behavior pose a genuine risk of violence. The work involves collecting and analyzing information about the individual’s statements, behavior, personal circumstances, and access to weapons, then producing an assessment that informs a protective response. The assessment distinguishes between transient threats (someone venting frustration online) and substantive threats (someone with the intent, psychological state, and capability to carry out violence). If you studied psychology, criminology, or behavioral science, threat assessment is the most direct application of that knowledge in an OSINT-adjacent field. These roles exist in corporate security departments (assessing threats against employees and facilities), law enforcement (assessing threats against public officials or in school and workplace violence contexts), and government agencies. The Association of Threat Assessment Professionals (ATAP) provides training and certification that are recognized entry pathways, and the field is growing in the private sector as more companies formalize their threat management programs.
Counterintelligence analysis combines behavioral understanding with OSINT research to identify and assess threats from foreign intelligence services, insider threats, and other adversaries attempting to penetrate or compromise an organization. A counterintelligence analyst tracks which employees are exhibiting behaviors associated with insider threat risk, which foreign entities are targeting the organization’s personnel or technology, and how those threats are evolving. These roles exist primarily in government agencies and defense contractors, though corporate counterintelligence programs are growing at technology companies and other organizations that handle sensitive intellectual property.
Insider threat analysis (also covered in the cyber section) sits at the intersection of behavioral science and technical monitoring. Insider threat analysts track the behavioral and technical indicators that an employee may be misusing their access, combining endpoint monitoring data with an understanding of why people betray trust. An insider threat analyst might triangulate anomalies in network access logs (downloading large volumes of data outside normal business hours) with behavioral indicators identifiable through open sources (expressions of severe financial distress, ideological radicalization, or unexplained lifestyle changes). The field is growing rapidly in both government and private sector as organizations recognize that external cyberattacks and internal threats require different detection methods.
What This Map Doesn’t Cover
This is a map of career fields, not a roadmap for getting hired. Knowing that a field exists is the first step, but each of these career paths has its own hiring process, qualification requirements, and professional culture. Some require clearances, others require licenses or specific technical certifications, some value portfolio work over credentials, and some won’t look at you without a degree. A future article will address those specifics: what each field actually looks for in candidates, which certifications matter and which don’t, and how to position skills from one background for a role in another.
This map also focuses on fields where OSINT skills are central to the work. Plenty of other positions use OSINT as one tool among many (military intelligence officers, diplomats, policymakers, corporate executives who consume intelligence products), but those roles aren’t built around OSINT as a primary skill set. The fields listed here are the ones where your ability to find, evaluate, and make sense of open-source information is the core of what you’re being paid to do.
If you’re trying to figure out where you fit, start with what you’re already good at and what kind of work you actually want to do day-to-day. The field is broad enough that there’s almost certainly a career path that matches your skills and interests. Once you know what to search for, you can find it.
Bonus: OSINT Job Spreadsheet
To go with this article, I put together a spreadsheet with 79 real job listings across all 12 categories. Each entry includes the employer, location, job title, a link to the posting, and the OSINT-related keywords from the job description. The listings are organized by career field so you can go straight to the categories that interest you.
Osint Jobs20KB ∙ XLSX fileDownloadDownloadA heads-up: job listings are transient. Some of these may be closed by the time you see them. That’s fine. The value isn’t in any individual posting; it’s in the patterns. The keywords, qualifications, and job descriptions show you what employers in each field are actually looking for, how they describe the work, and what language they use. Even a closed listing can teach you which skills to develop, which certifications get mentioned, and what to search for when you’re ready to apply. Use this as a reference for employers, keywords, and job title patterns rather than expecting every link to still be live. Good luck!!
Originally published on Substack
View on Substack →